Problem
You are trying to create a token on behalf of a service principal, using /2.0/token-management/on-behalf-of/tokens in the REST API but are getting a PERMISSION_DENIED error.
{
"error_code": "PERMISSION_DENIED",
"message": "User xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx does not have permission to use tokens."
}Cause
This happens when the service principals are assigned to a user group that has token usage disabled.
Solution
Your workspace admin should enable token usage for the user group that contains the service principals.
Enable token usage via the UI
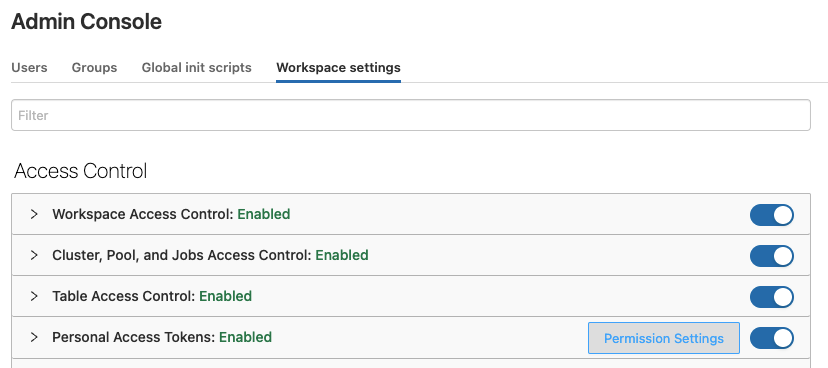
- Click Settings in the left hand menu.
- Click Admin Console.
- Click the Workspace settings tab.
- Click Permission Settings in the Personal Access Tokens field.
- Add the groups that need token access in the Token Usage window.
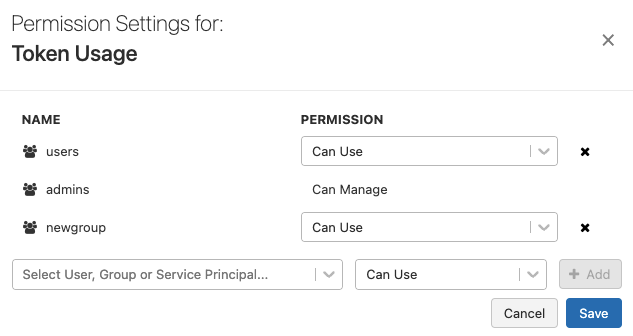
- Remove any groups that should not have token access.
- Click Save to apply the changes and close the window.
Enable token usage via the REST API
- Review the token permissions API settings.
- Use this sample code to update the token permissions.
- Replace the following values in the sample code before running it on your local machine:
- <admin-access-token> - Admin personal access token.
- <user-group-name> - The name of the user group to grant token access permission. You can add multiple group entries if needed.
- <workspace-url> - Replace this value with your Workspace URL.
curl --location --request PATCH 'https://<workspace-url>/api/2.0/preview/permissions/authorization/tokens'; \
--header 'Authorization: Bearer <admin-access-token>' \
--header 'Content-Type: application/json' \
--data-raw '{
"access_control_list": [
{
"group_name": "<user-group-name>",
"permission_level": "CAN_USE"
},
{
"group_name": "<user-group-name>",
"permission_level": "CAN_USE"
}
]
}'